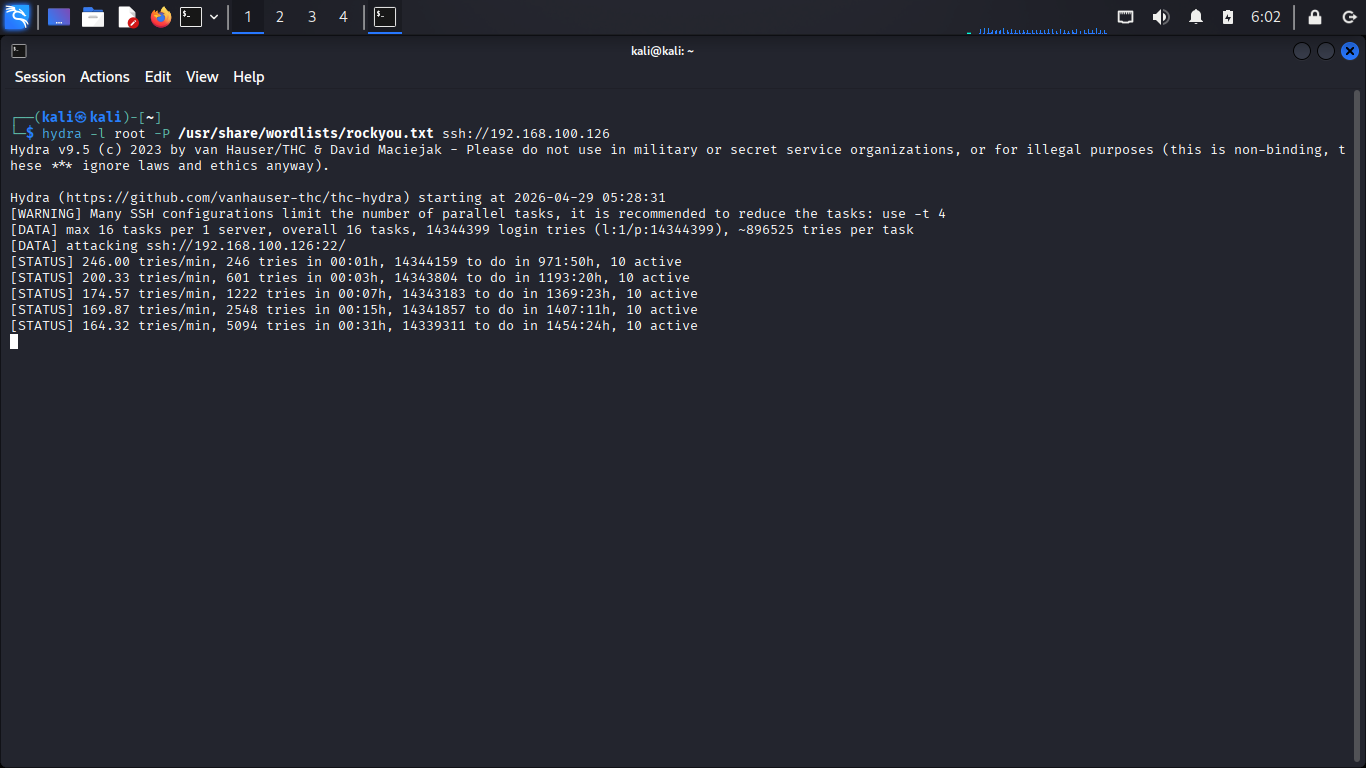
A brute-force attack was simulated using Hydra against the SSH service on the target system. The tool generates repeated login attempts using a password wordlist, creating high-frequency authentication failures typical of brute-force credential attacks.
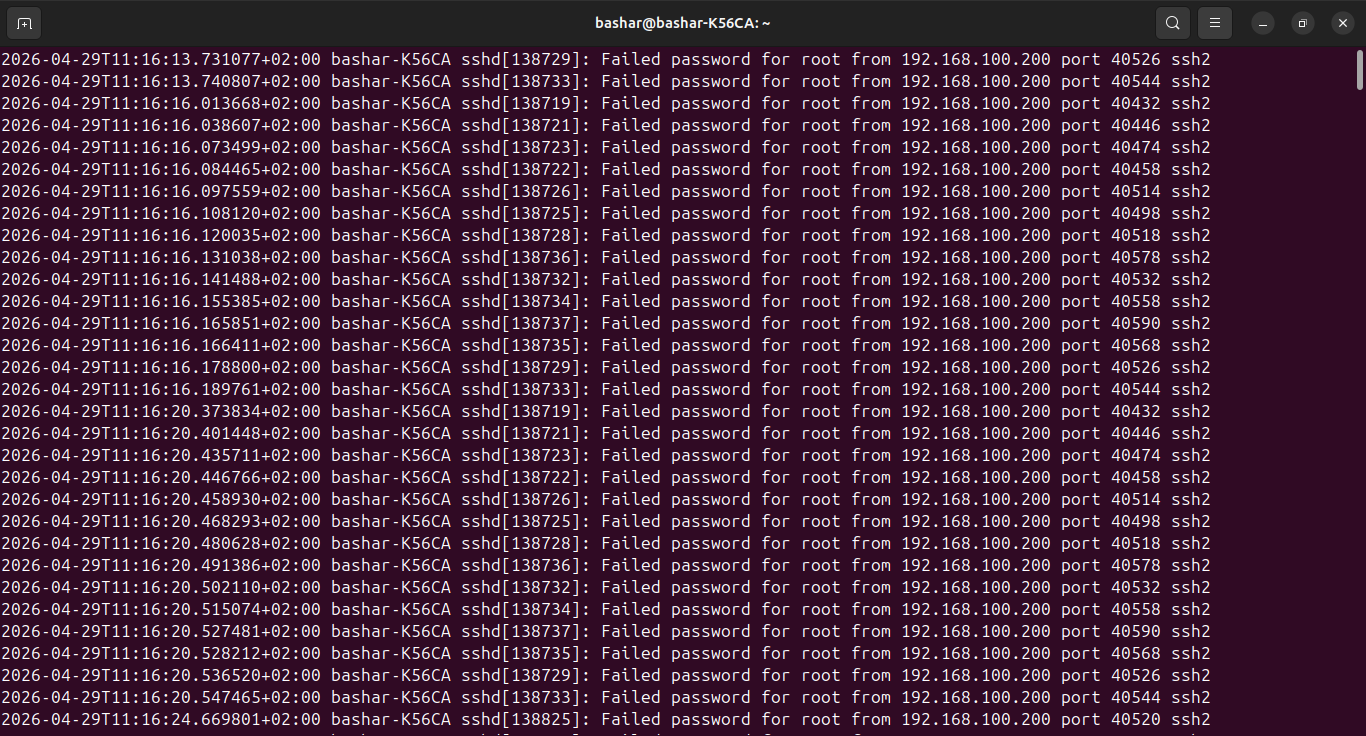
The system authentication log (/var/log/auth.log) shows multiple failed SSH login attempts from a single source IP within a short timeframe, indicating automated activity. This confirms that the attack reached the host and provides raw evidence of brute-force activity.
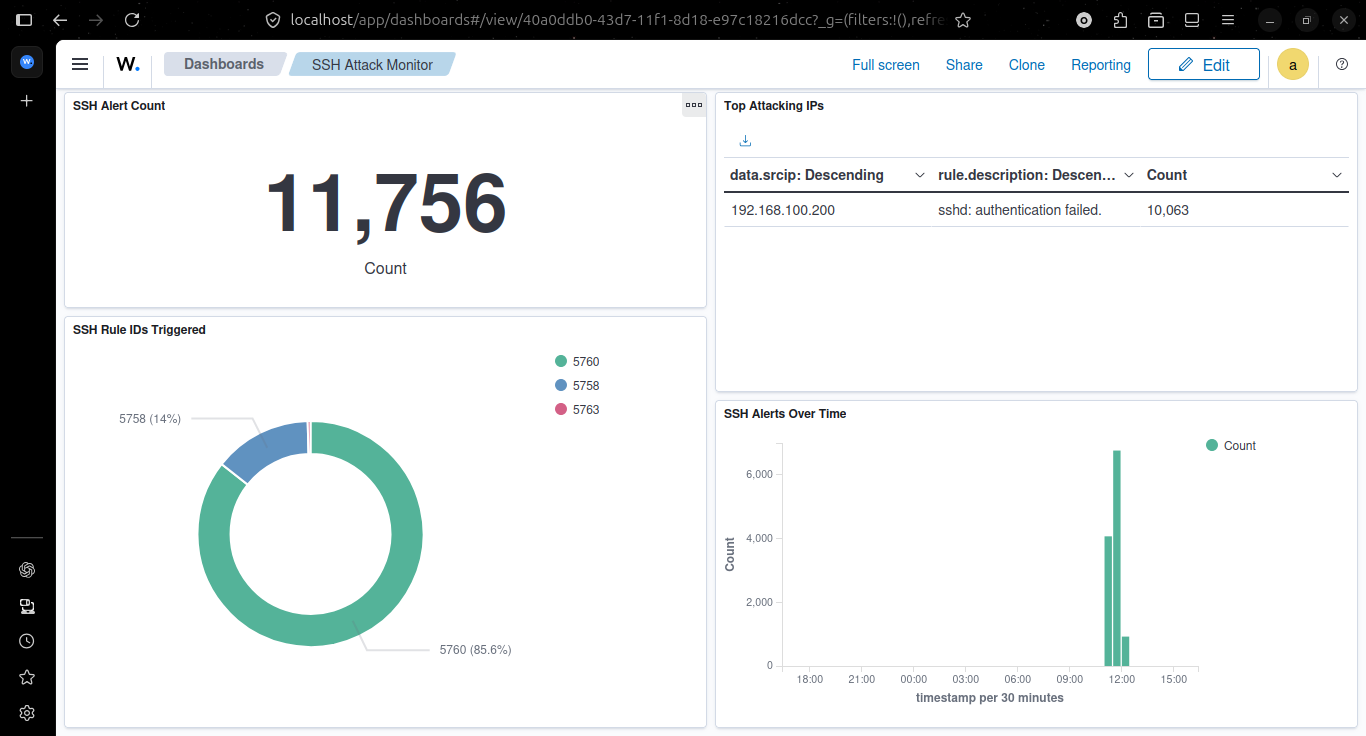
A custom Wazuh dashboard visualizes the attack activity, including alert volume over time and the originating IP address responsible for the activity. The spike in alerts during the attack window confirms that the SIEM successfully ingested and identified the abnormal authentication behavior.
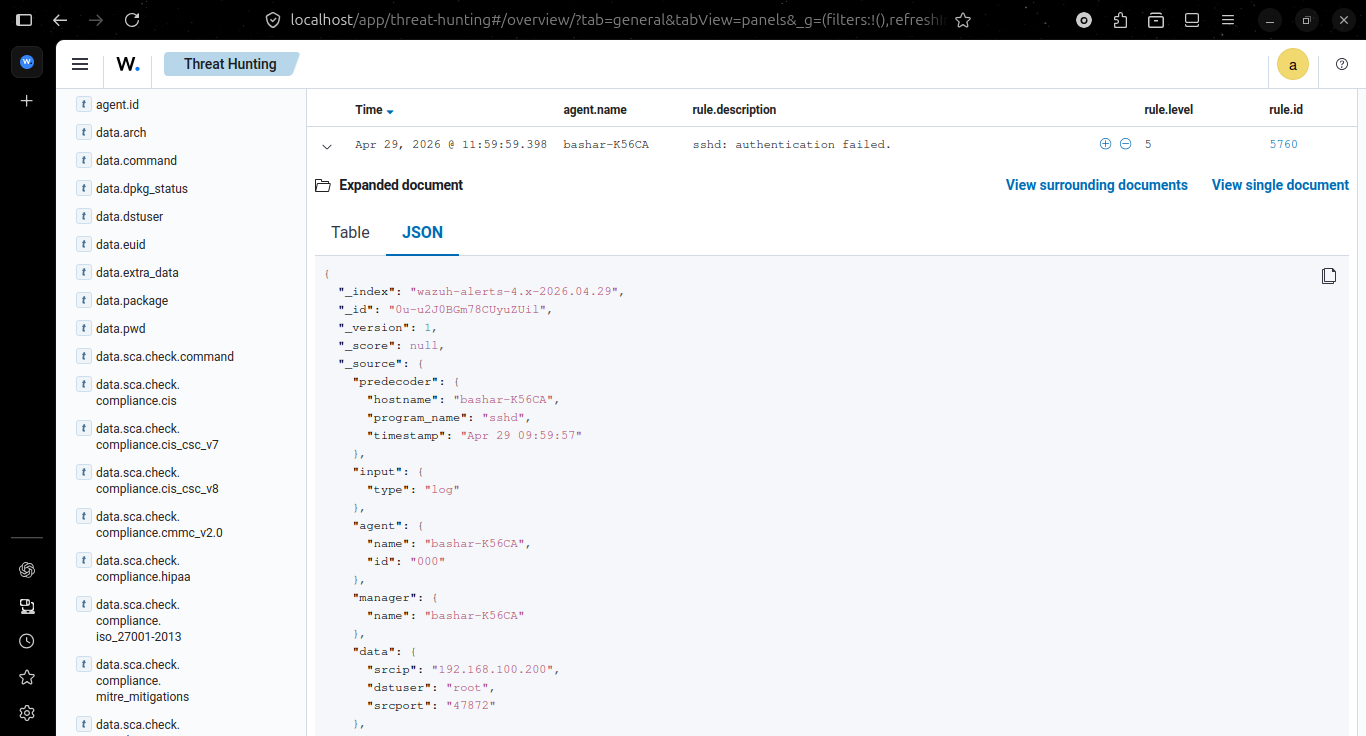
Expanding an individual alert reveals key details such as the rule triggered, source IP, timestamp, and MITRE ATT&CK classification (T1110 – Brute Force). This confirms the nature of the activity and provides the necessary context to validate and investigate the threat.
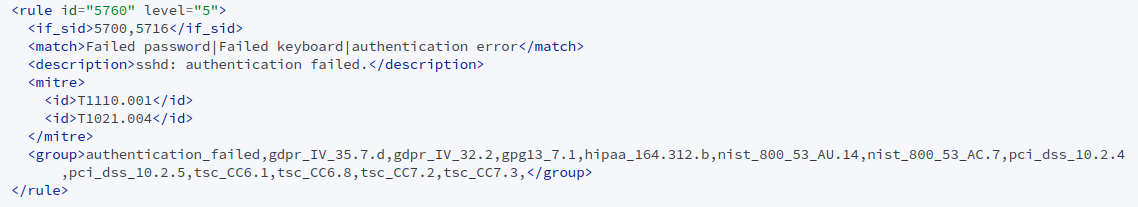
Rule 5760 triggers on each failed SSH authentication attempt. During the attack, repeated failures generate a high volume of alerts, forming the base signal used to identify abnormal authentication patterns during the attack.